How Does Technology Affect Employee Engagement?
These days, virtually all businesses use digital technology to help their employees communicate, collaborate, and access important data. Such technology is designed to help…
What Should Remote Workers Know About Cybersecurity?
Ever since the COVID-19 pandemic, work-from-home arrangements have been commonplace. In many ways, remote work is a win-win: Employees love flexibility and the lack of…
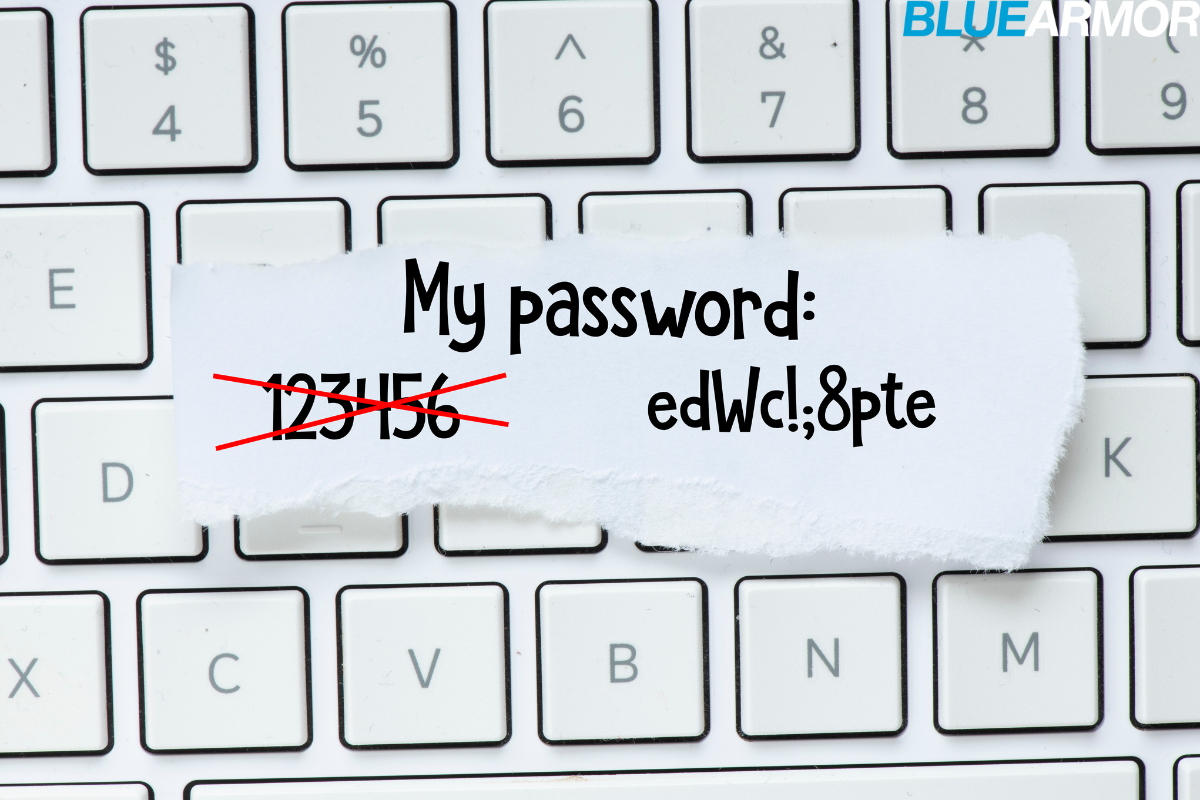
Best Practices for Strong Passwords
Most of us deal with passwords each and every day, using them to protect everything from our email accounts to our online banking profiles. When it comes to keeping hackers…
Essential Steps to Secure Your Devices
Any time you go online, there’s at least some chance that you’ll run afoul of a hacker or another type of online criminal, potentially losing valuable data or even falling…
What are Your Biggest Cybersecurity Risks?
Cybersecurity is not a new concept. Since the earliest days of the Internet, business organizations have faced an acute need to protect their data and to avert online…
How to Identify the Signs of Smishing
Imagine that you’re out running errands, perhaps pushing your cart through the aisles of your favorite grocery store. Your pocket vibrates. You reach down to see that you…
How to Promote Cybersecurity While Traveling
Summer vacation season will be here before you know it. And while there’s much to look forward to in this long stretch of fun and sun, it’s important to remember that summer…
Cybersecurity Tips for Seniors
For older adults, the Internet can be an invaluable source of information, community, and connection. Unfortunately, it can also be an avenue for potential criminality. Many…
Cybersecurity Basics for Construction Companies
As we’ve noted in the past, construction companies are uniquely vulnerable to cybersecurity breaches… and the effects can be financially ruinous. That’s the bad news. The…
How Can Employees Prevent Phishing Attacks?
For small and medium-sized businesses, cyberattacks are tragically common. One of the most common cyberattacks of all is the phishing scam. According to a Proofpoint survey,…